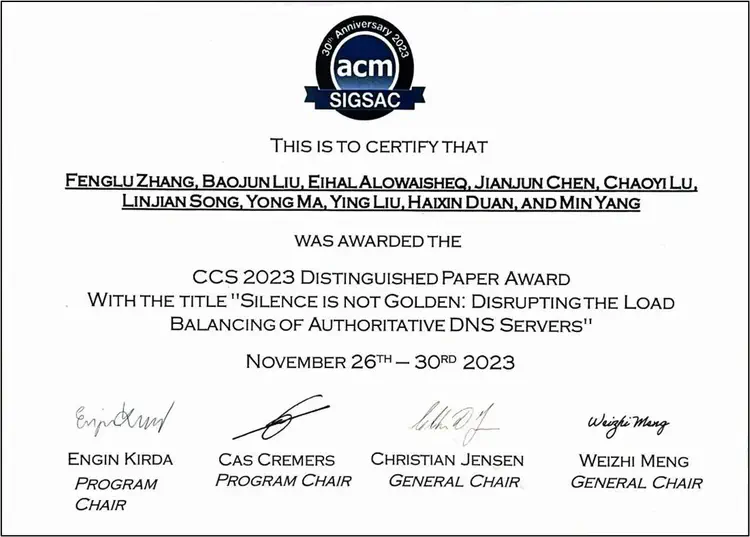
* ACM CCS Distinguished Paper Award.
* Community event contribution: OARC 41 and ICANN APAC DNS Forum 2023
Abstract
Authoritative nameservers are delegated to provide the final resource record. Since the security and robustness of DNS are critical to the general operation of the Internet, domain name owners are required to deploy multiple candidate nameservers for traffic load balancing. Once the load balancing mechanism is compromised, an adversary can manipulate a large number of legitimate DNS requests to a specified candidate nameserver. As a result, it may not only bypass the defense mechanisms used to filter malicious traffic that can overload the victim nameserver, but also lowers the bar for DNS traffic hijacking and cache poisoning attacks.
In this study, we report a class of DNS vulnerabilities and present a novel attack named Disablance. Our proposed attack allows adversaries to stealthily sabotage the DNS load balancing for authoritative nameservers at a low cost. By just performing a handful of crafted requests, an adversary can manipulate a given DNS resolver to overload a specific authoritative server for a period of time. Therefore, Disablance can redirect benign DNS requests for all hosted domains to the specific nameserver and disrupts the load balancing mechanism. The above attack undermines the robustness of DNS resolution and increases the security threat of single point of failure. Our extensive study proves the security threat of Disablance is realistic and prevalent. First, we demonstrated that mainstream DNS implementations, including BIND9, PowerDNS and Microsoft DNS, are vulnerable to Disablance. Second, we developed a measurement framework to measure vulnerable authoritative servers in the wild. 22.24% of top 1M FQDNs and 3.94% of top 1M SLDs were proven can be the victims of Disablance. Our measurement results also show that 37.88% of stable open resolvers and 10 of 14 popular public DNS services can be exploited to conduct Disablance, including Cloudflare and Quad9. Furthermore, the critical security threats of Disablance were observed and acknowledged through in-depth discussion with a world-leading DNS service provider. We have reported discovered vulnerabilities and provided recommendations to the affected vendors. Until now, Tencent Cloud (DNSPod) and Amazon have taken action to fix this issue according to our suggestions.